by Susan Cisco

An organization’s retention schedule prescribes retention for its “official records.” Drafts, duplicates, convenience copies, records with expired retention, etc. can account for four to five times the volume of the official records. A large volume of unnecessary information puts an organization at risk for non-compliance with privacy and other recordkeeping requirements, exponential increases in storage requirements, and increased litigation risk from unnecessary production and review of obsolete content in discovery efforts. Fortunately, there’s a good strategy to overcome this chronic retention. An enterprise-wide Information Lifecycle Model (ILM) enables organizations to manage information consistently by categorizing it by lifecycle state.
Why do organizations retain useless information (non records)? For most, it is the fear of the unknown. Few organizations have an enterprise view of how much information there is, what it is, who its owners are, what it is used for, or its value. The consequences of not knowing can be disastrous, yet most organizations still lack consistency in applying retention controls to information.
To manage the risk and costs from over preservation, organizations need a sustainable policy and defensible process for destroying/deleting unnecessary information. Everything needs a retention period, which is defined in an Information Lifecycle Model (ILM), asuccession of conditions through which information is processed from creation or receipt to its final disposition.
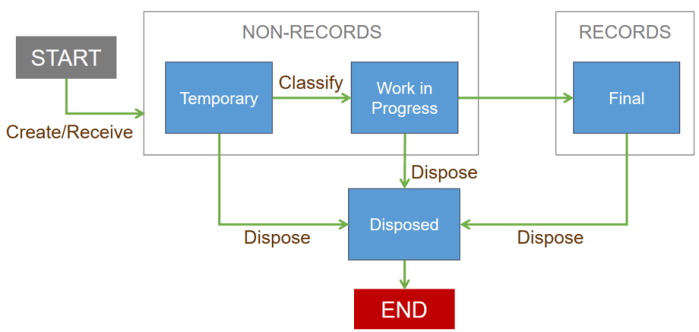
All states (Temporary, Work in Progress, Final, and Disposed) in the ILM have a transition to the “Disposed” state which is usually destruction or deletion. Within the ILM, each state has a rule for retention, which is the maximum amount of time that a piece of content can exist in that state. Therefore, information in the Temporary state may have a retention period of 90 days (from the last modified date) while information in the Work in Progress may have a retention of two years (from the last modified date).
Establishing the retention periods is best done in a workshop setting, with stakeholders from technical and non-technical groups. The result is consistent information governance combined with consistent employee expectations for how they should participate in the management and retention of information.
Use-Right-Away Tips
- Start by identifying high-risk information. Conduct an inventory of high-risk information such as confidential or personally identifiable information, intellectual property, and information needed in case of a disaster. A spreadsheet is helpful for documenting the location and format of the information, its lifecycle state, and how it is used.
- Review findings with leadership. Present findings to leadership and recommend ILM as a tool for reducing risk and achieving compliance while maximizing the information’s value to your organization.
Catch Susan and other spectacular speakers at IAAP Summit 2019 in National Harbor, Maryland (just a short distance from Washington D.C.). Find out why IAAP Summit is the go-to conference for office and administrative professionals year-in and year-out.
Susan Cisco has more than 35 years’ experience in the RIM/IG profession as a practitioner, educator, and consultant. Her seminal work in developing the Big Bucket Approach is key to simplifying retention management. She holds an MLS degree and a Ph.D. from the University of Texas at Austin. She is a CRM and an ARMA Fellow.

